Ransomware: Prevention and Protection

When it comes to ransomware (and for that matter, all malware), prevention is the best course of action. To put it simply, the aim is to make sure your computer is NOT an ideal target — a porcupine rather than a fish. A contingency plan is crucial too: that consists of having your data backed-up, meaning would-be attackers will have far less leverage over you. Follow these guidelines to help avoid viruses in the first place.
Ransomware Prevention
Emails
- Scan all email attachments for malware. Be careful about opening attachments from unknown sources.
- Avoid opening executable files included as attachments.
- Regularly update email apps — as well as web browsers and operating systems.
- Never click on links in the body of email messages.
- Double-check the sender’s name to confirm that an email is from a legitimate source.
- Beware of signs that indicate phishing such as: grammatical errors, suspicious attachments, and weird domain names.
Phone and Apps
- NEVER jailbreak phones.
- Download apps/software from well-known, legitimate stores only, such as Google Play and the App Store. Only verified apps should be installed.
- Review the app before you install. Check reviews, app downloads and requested permissions.
- Never insert unknown USB drives or floppy disks into your computer.
- When using public Wi-Fi, use a VPN such as ExpressVPN or VPN Proxy One Pro.
- Keep apps updated as well. Be sure to use the latest versions to keep security up to date.
Ransomware Protection: Product Solutions
The best thing you can do to protect yourself is to follow the preventative measures listed above, and to install a trusted antivirus product — Trend Micro, Norton or Kaspersky are good options.
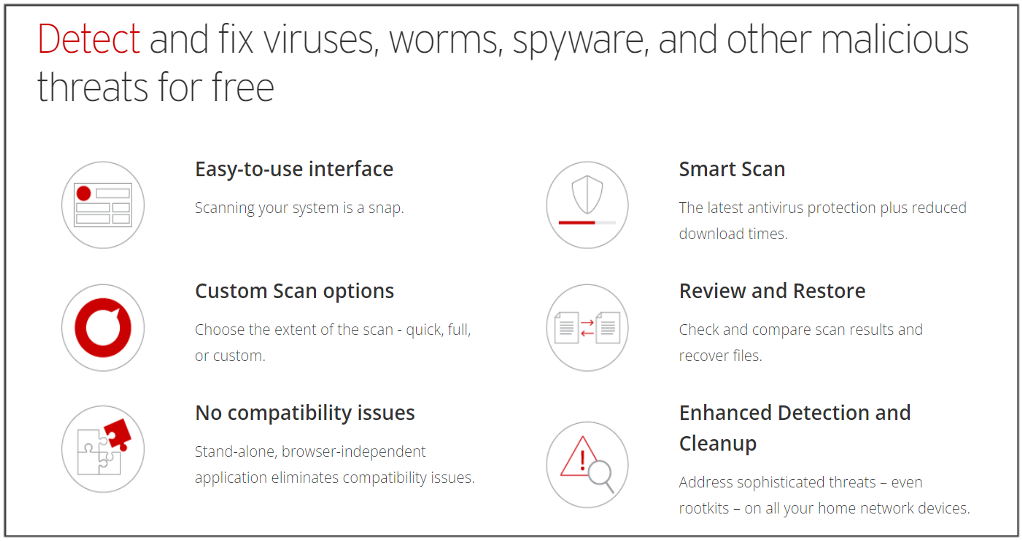
Trend Micro HouseCall is a very good, free scan & fix product. It guards against and cleans up cyberthreats, including viruses, worms, Trojans, and spyware. You could also investigate their Antivirus+ Security, which offers:
- Real-time Web Threat Protection
- Cloud-based AI, Smart Protection Network™, which keeps track of evolving threats
- Ransomware protection
- Anti-phishing/spam software
- Performance Optimization
- Folder shields that protect your most sensitive date
Ransomware Removal
In the event of suspected malware:
1. Disconnect your device from the internet. You can do this by disabling Wi-Fi on your device or turning off your router.
2. Start up your computer in Safe Mode. This lets it use only the most essential apps. Be aware that the instructions for how to boot in Safe Mode will differ depending on your device.
3. Look for any suspicious apps and remove them. See something you don’t recognize (along with a recent installation date)? Best to uninstall.
4. Run one of the virus scans we mention above. A good virus scanner like HouseCall should resolve and remove the issue.
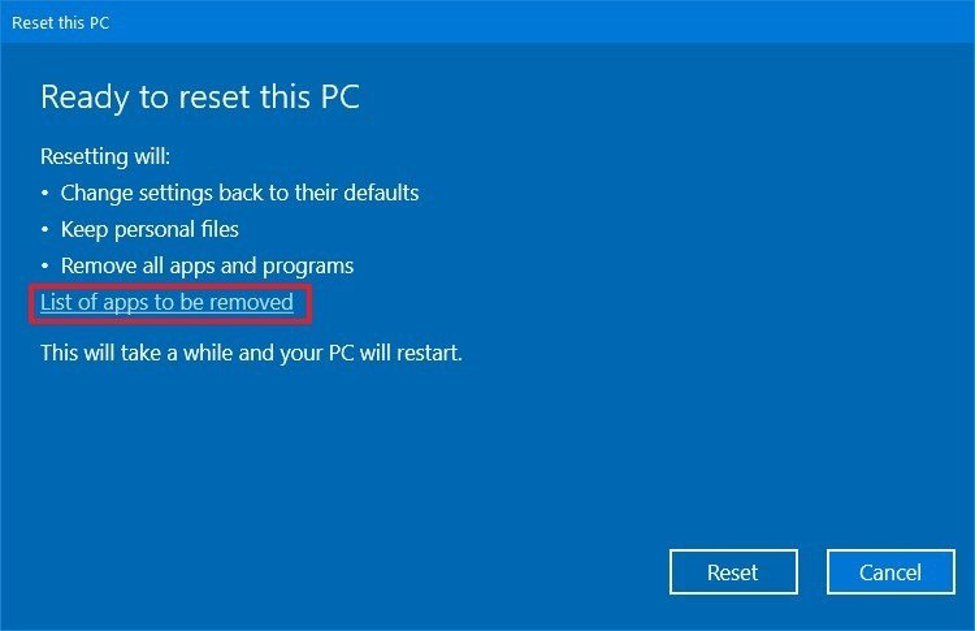
5. Follow the scan with a Restore action to your device’s default settings. (It is a good habit to regularly back-up data and create “restore points”.
6. If none of the above have worked, your only remaining option (barring a bespoke professional service) is to perform a full System Restore. Be aware though, that this will delete all personal data, settings and files.
Ten Dos and Don’ts
We will end here with ten dos and don’ts in the unfortunate event of a ransomware attack.
1. Do not pay the ransom. It only encourages these attacks — and there’s no guarantee your files will be released.
2. Restore any impacted files from a trusted backup.
3, Do not provide personal information when answering emails, unsolicited phone calls, text or instant messages.
4. Use antivirus software and a strong firewall. It’s important to make sure it’s from a reputable company because of all the fake software out there — which is often malicious itself!
5. Do employ content scanning and filtering on your mail servers. Inbound e-mails should be scanned for known threats. Trend Micro Check is a good product for this.
6. Do make sure that all systems and software are up-to-date with relevant patches.
7. If traveling, tell your work’s IT department, especially if you’re going to be using public Wi-Fi. Be sure you know how to connect to the company’s Virtual Private Network (VPN).
8. Be aware that exposing intellectual property is against most corporate policies. It’s not simply unethical — it can land you in court.
9. Read your company’s Acceptable Electronic Use (AEU) policy. If you’re unsure about an email’s legitimacy, contact your IT department.
10. When backing-up to cloud services, be sure to talk to your IT department first, for a list of acceptable cloud solutions.
We hope this article and its preceding part have shed some light for you. If you’ve found this content useful and/or interesting, please do SHARE with family and friends to help keep the online community secure and protected.