Malware infects MacOS using Zero-day vulnerability – XCSSET

The malware XCSSET initially posed a danger to Xcode developers when it cleverly took advantage of two previously unknown macOS vulnerabilities within Safari. However, the developers of this malware weren’t content to stop there. They created new strains which they have used to launch a full-fledged malware campaign. The new strains have the capability of stealing confidential data, covertly taking screenshots, remotely accessing microphones and webcams, and installing ransomware.
Let’s dive into the murky waters and find out everything you need to know about this ongoing malware campaign.
How does XCSSET spread?
The threat researchers at Trend Micro first identified the malware through an unusual infection related to Xcode developer projects. Xcode is an integrated development environment (IDE) for macOS used for software development within the Apple ecosystem. It is available for free on the Mac App Store.
A sample of an Xcode project is shown below.
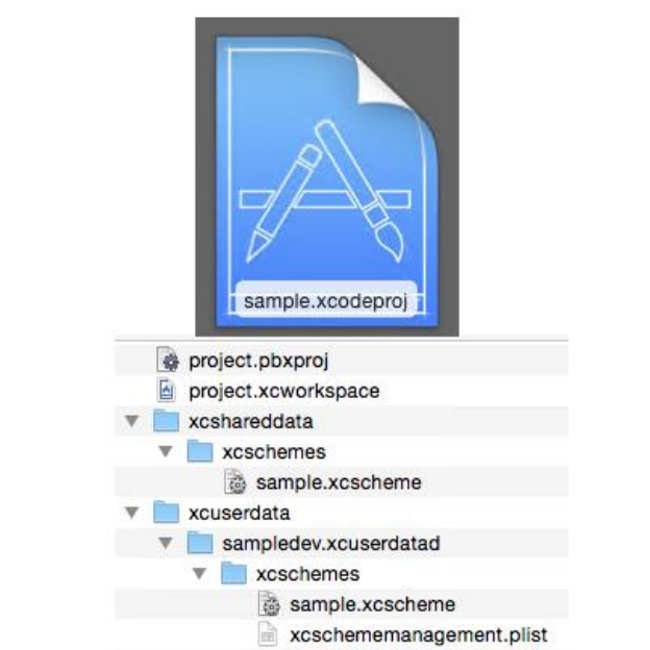
Many developer’s Xcode projects were found to contain the source malware — which led to a rabbit hole of malicious payloads. This resulted in tons of developers unwillingly spreading the malware as they shared their projects via platforms such as GitHub, leading to a supply-chain-like attack for those who use these platforms.
At this point, how XCSSET malware burrows itself into local Xcode projects is not yet know.
What does the XCSSET MacOS Malware do?
XCSSET malware exploits Safari vulnerabilities
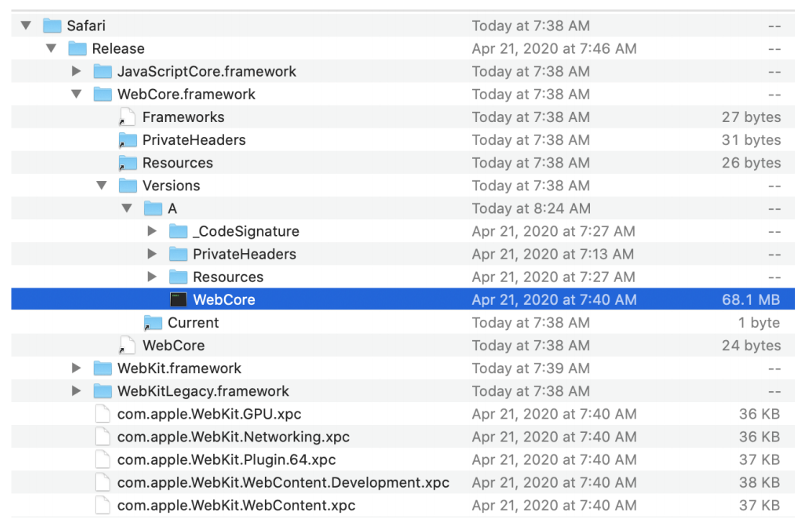
It compromises the Safari browser through two previously undiscovered vulnerabilities.
The first of the zero-day flaws bypass the data vault to dump and steal Safari cookies.
The second abuses the development version of Safari to carry out universal cross-site scripting (UXSS) attacks and inject various JavaScript payloads. This allows the malware to compile a rogue Safari app and install it on the infected computer.
Steals information from apps and Chrome-based browsers
XCSSET doesn’t only target Safari. It also exploits the browser debugging mode of Chrome-based browsers. This allows hackers to manipulate and replace Bitcoin (BTC), Ethereum (ETH), Tether (USDT), and other cryptocurrency addresses. It can also take screenshots of the victim’s desktop and hijack their web browser .
It can also collect credit card and Apple ID information linked to the Apple App Store and steal credentials from Google Chrome, Yandex, PayPal, and other platforms.
Additionally, it can access user data from apps such as QQ, WeChat, Telegram, and Skype, while also controlling their security and privacy settings.
Investigations have revealed that stolen information mainly came from China, closely followed by India, but many people from the United States, Ukraine, Pakistan, and the Philippines have been affected, too.
Operates as traditional ransomware
XCSSET malware has a critical set of ransomware modules that most often remain inactive, but if a victim is deemed to be a good target for extorsion, they have the potential of executing.
Imitate apps for Big Sur (MacOS 11)
The updated XCSSET malware has adapted to the newly released Big Sur (MacOS 11) and can circumvent its new security policies.
The malware downloads packages from its own command and control server that come pre-signed with ad-hoc signatures to launch these fake apps.
For more technical analysis of this malware, you can refer to Trend Micro’s blog and technical brief.
How can Mac users avoid XCSSET infection?
Since XCSSET is primarily spreading through Xcode projects, if you are a developer, you should only download projects from trusted sources. However, not only developers can become victims. XCSSET can also spread through infected apps, so it’s essential to not download apps from untrusted or suspicious sources.
Given the potentially destructive coverage of the malware abuse and damaging payloads, the best method of defense is an up-to-date anti-malware program.
Antivirus One is your personal cybersecurity companion. It offers live antivirus monitoring to protect your Mac from adware, ransomware, spyware, and all kinds of malware attacks. Antivirus One has Real Time Detection capabilities, providing you the protection you need against malware and other threats 24/7. Its virus scanner and remediation algorithm safeguard every part of your system and fully protect your security and privacy, and it’s the perfect tool for keeping your digital wallets and keychains safe and secure.
To keep your Mac safe, download Antivirus One from the Mac App Store.